- 0286.6706123
Ngày đăng: 27/03/2023
With the rapid development of modern science and technology, the structure of my country’s medical system has been continuously improved, and the number of large and valuable medical equipment and instruments in large and medium-sized hospitals has also been increasing. High-quality, sophisticated and sophisticated medical equipment has become an important symbol of hospital modernization. In reality, there are various problems in medical radiology business systems and business terminals. The radiological terminals are basically in a “streaking” state. Once a security incident occurs, the business will be paralyzed, which will cause serious impacts and major losses.
From 2018 to 2020, multiple medical group equipment has been exposed to the risk of security vulnerabilities on the Internet:
1. In January 2020, a security breach was discovered in the patient monitoring equipment of a medical group, which could lead to DOS attacks and malware attacks.
2. In October 2019, the US Food and Drug Administration warned that medical devices using IPnet components had a large number of serious vulnerabilities that could lead to remote hacker attacks.
3. In April 2018, medical imaging equipment (MID) had multiple high-risk vulnerabilities that were vulnerable to cyber attacks.
The use and operation and maintenance of high-end medical equipment often require technical personnel from equipment manufacturers to provide operation guidance and inspection and maintenance. At present, hospitals often update and maintain equipment remotely through the external network. Once connected to the external network, there will be certain Cybersecurity risks:
1. The equipment of the radiology department is managed by the equipment department, and the information department has no right to operate, and the equipment department is relatively lack of safety awareness. The equipment is easily infected by viruses and forms internal network transmission;
2. In view of the characteristics of the medical equipment system, it is impossible to install third-party anti-virus software, and the anti-virus software on the workstation often kills by mistake, causing the equipment to be in a streaking state for a long time;
3. The security strategy is complex. In hospitals, ACL strategies are often configured through traditional switches to prevent the spread of viruses, but the configuration and use are complicated.
Disadvantages of traditional solutions:
Traditional solutions generally focus on exports and neglect intranets. The main problems are as follows:
1. Security mechanisms are difficult to sink: security devices are generally deployed in key locations such as borders and data centers. Security mechanisms cannot extend to the inside of the network, cannot sink security mechanisms, and cannot defend against new threats and variant viruses.
2. It is difficult to guarantee business operation and maintenance: the network level cannot effectively identify and distinguish traffic and threats (viruses, attacks, etc.), security control strategies cannot be implemented, operations are not visible, and operation and maintenance are difficult to achieve.
East-west Traffic Security Scheme:
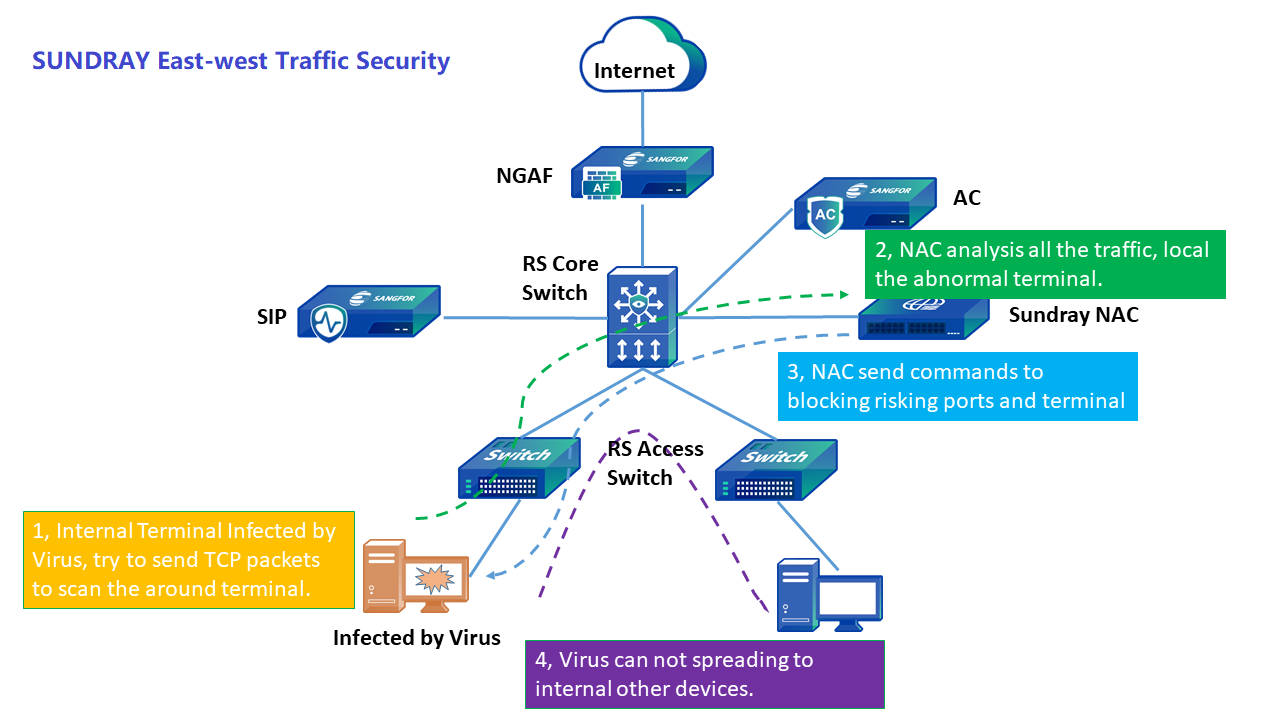
Sundray Smart Switch responds to new threats of variant viruses and proposes east-west traffic security solutions:
1. Business black and whitelist, risk port blocking
Block the blacklist of known risky ports to fundamentally eliminate risks; for secure ports, you can configure a whitelist to allow specific access to services.
2. Quickly locate abnormal terminal infected with Viruses
The Smart Switch is linked with the Sundray NAC to identify and locate the source of viruses and attacks in real time through the FSE traffic security engine.
3. The core business can run “with disease”
The Smart Switch is linked with the Sundray NAC to only let the normal business traffic of the radiation terminal pass, and all other traffic is blocked. When the terminal is inconvenient for anti-virus treatment, this method can be used to meet the normal business development and avoid the horizontal spreading of the virus.
Sundray Smart Switch Network Advantages:
1. Network security situation analysis
The overall security situation is presented, and risk services, risk terminals, interception conditions, attack conditions, etc. are located.
It can clearly show the exchange of visits between areas and roles, and help administrators perform security analysis.
2. Accurate traceability of security threats
Detailed security event logs can be searched directionally through options such as time, event type, attacker’s MAC, access point, and switch.
Accurate to the terminal user name, IP, MAC address, switch port, service type, risk service, risk terminal, interception situation, attack situation, etc.
Sundray Smart Switches respond to the new threats of variant viruses and propose Sundray East-west Traffic Security solutions, which are safe and visible and risk barriers. They are favored by the medical industry and have now served thousands of hospitals.